- October 8, 2020
- Posted by: administrator
- Category: Anti-Virus & Firewall, Security News
Cybersecurity researchers have spotted a rare kind of potentially dangerous malware that targets a machine’s booting process to drop persistent malware.
The campaign involved the use of a compromised UEFI (or Unified Extensible Firmware Interface) containing a malicious implant, making it the second known public case where a UEFI rootkit has been used in the wild.
According to Kaspersky, the rogue UEFI firmware images were modified to incorporate several malicious modules, which were then used to drop malware on victim machines in a series of targeted cyberattacks directed against diplomats and members of an NGO from Africa, Asia, and Europe.
Calling the malware framework “MosaicRegressor,” Kaspersky researchers Mark Lechtik, Igor Kuznetsov, and Yury Parshin said a telemetry analysis revealed several dozen victims between 2017 and 2019, all of whom had some ties to North Korea.
UEFI is a firmware interface and a replacement for BIOS that improves security, ensuring that no malware has tampered with the boot process. Because UEFI facilitates the loading of the operating system itself, such infections are resistant to OS reinstallation or replacement of the hard drive.
“UEFI firmware makes for a perfect mechanism of persistent malware storage,” Kaspersky said. “A sophisticated attacker can modify the firmware in order to have it deploy malicious code that will be run after the operating system is loaded.”
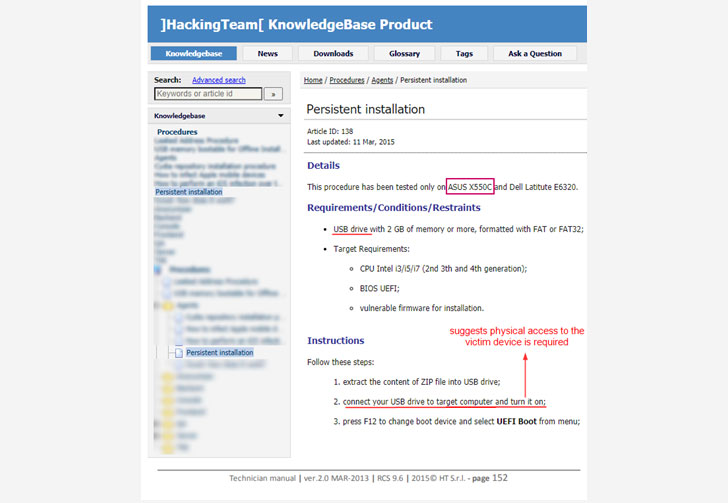
That’s exactly what this threat actor appears to have done. Although the exact infection vector employed to overwrite the original firmware remains unknown at this stage, a leaked manual suggests the malware may have been deployed through physical access to the victim’s machine.
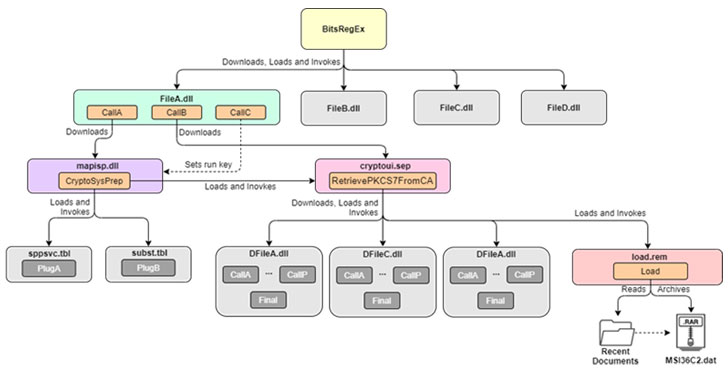
The new UEFI malware is a custom version of the Hacking Team’s VectorEDK bootkit, which was leaked in 2015 and has since been available online. It’s used to plant a second payload, called the MosaicRegressor — “a multi-stage and modular framework aimed at espionage and data gathering” that consists of additional downloaders to fetch and execute secondary components.
The downloaders, in turn, contact the command-and-control (C2) server to grab next-stage DLLs in order to execute specific commands, the results of which are exported back to the C2 server or forwarded to a “feedback” mail address from where the attackers can collect the amassed data.
The payloads are transferred in a variety of ways, including via e-mail messages from mailboxes (“mail.ru”) hard-coded in the malware’s binary.
In some cases, however, the malware was delivered to some of the victims via spear-phishing e-mails with embedded decoy documents (“0612.doc”) written in Russian that purported to discuss events related to North Korea.
With regards to the identity of the threat actor behind MosaicRegressor, Kaspersky said it found multiple code-level hints that indicate they were written in Chinese or Korean and noted the use of Royal Road (8.t) RTF weaponizer, which has been tied to multiple Chinese threat groups in the past.
Lastly, Kaspersky found a C2 address in one of MosaicRegressor’s variants that have been observed in connection with Chinese hacker groups broadly known as Winnti (aka APT41).
“The attacks […] demonstrate the length an actor can go in order to gain the highest level of persistence on a victim machine,” Kaspersky concluded.
“It is highly uncommon to see compromised UEFI firmware in the wild, usually due to the low visibility into attacks on firmware, the advanced measures required to deploy it on a target’s SPI flash chip, and the high stakes of burning sensitive toolset or assets when doing so.”