- October 19, 2020
- Posted by: administrator
- Category: MicroSoft
The Emotet botnet has begun to use a new malicious attachment that pretends to be a message from Windows Update telling you to upgrade Microsoft Word.
Emotet is a malware infection that spreads through spam emails containing malicious Word or Excel documents. These documents utilize macros to download and install the Emotet Trojan on a victim’s computer, which uses the computer to send spam email and ultimately leads to a ransomware attack on a victim’s network.
After a short vacation, the Emotet malware returned to operation on October 14th and began blasting out malicious spam worldwide.
These spam campaigns pretend to be invoices, shipping information, COVID-19 information, information about President Trump’s health, resumes, or purchase orders, as shown below.
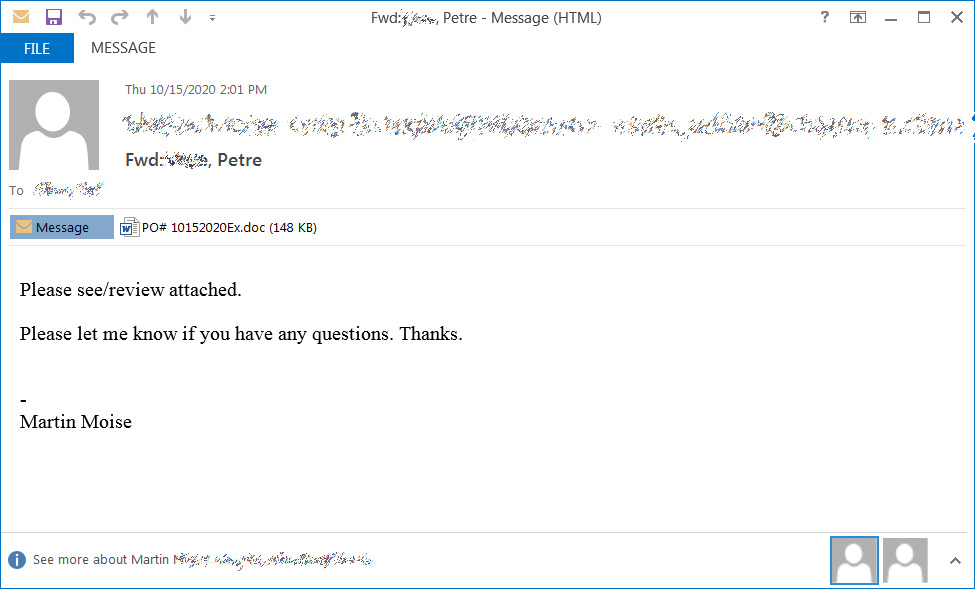
Attached to these spam emails are malicious Word (.doc) attachments or links to download one.
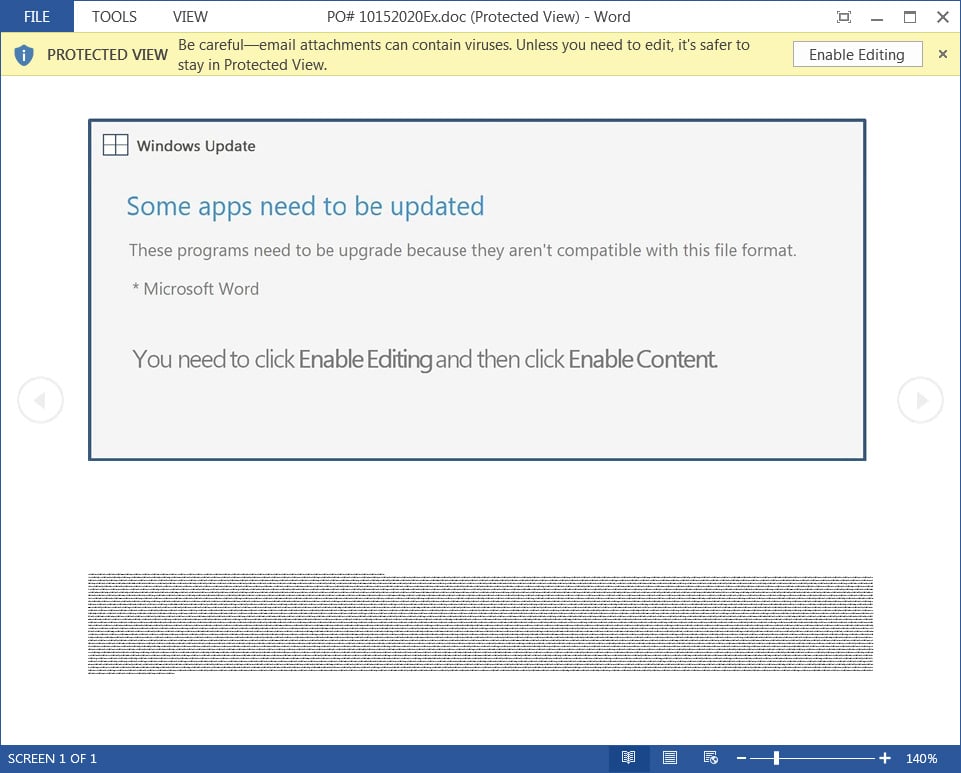
When opened, these attachments will prompt a user to ‘Enable Content’ so that malicious macros will run to install the Emotet malware on a victim’s computer.
To trick users into enabling the macros, Emotet uses various document templates, including pretending to be created on iOS devices, Windows 10 Mobile, or that the document is protected.
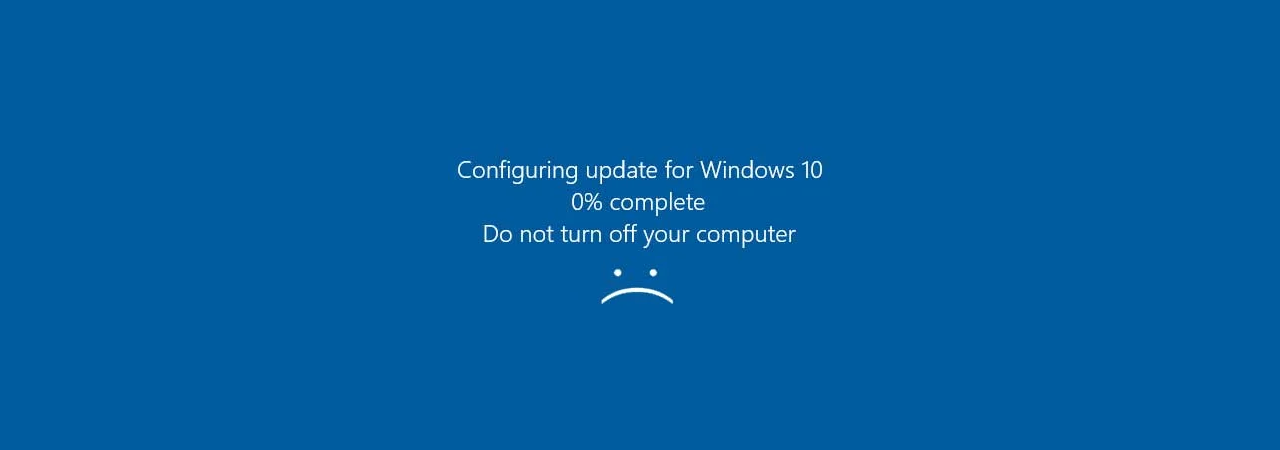
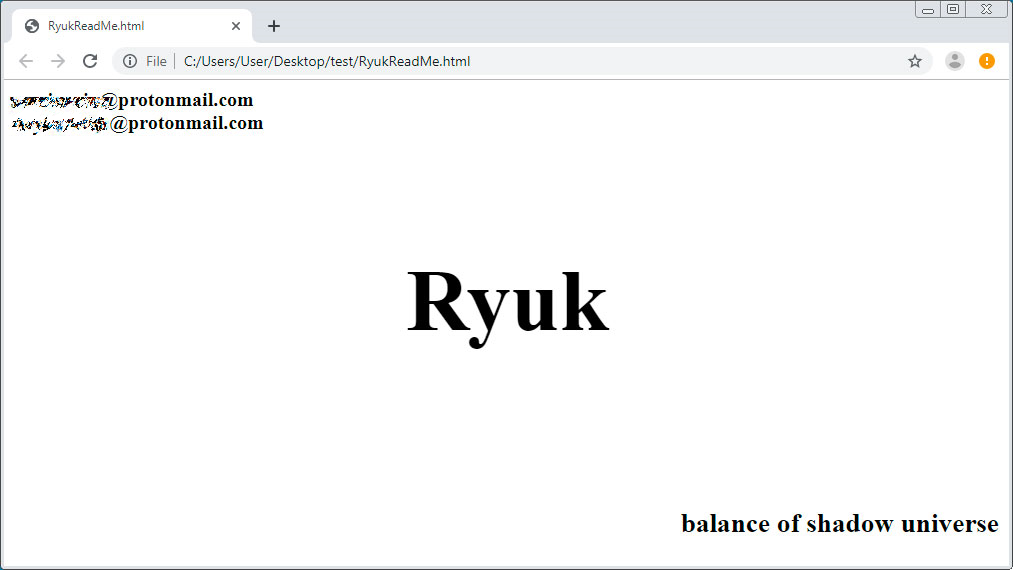
With its return to activity, Emotet switched to a new template that pretends to be a message from Windows Update stating that Microsoft Word needs to be updated before the document can be viewed.
- Windows Update
- Some apps need to be updated
- These programs need to be upgrade because they aren’t compatible with this file format.
- * Microsoft Word
- You need to click Enable Editing and then click Enable Content.
To update Word, the message tells the user to click on the Enable Editing and Enable Content buttons, which will cause the malicious macros to fire off,
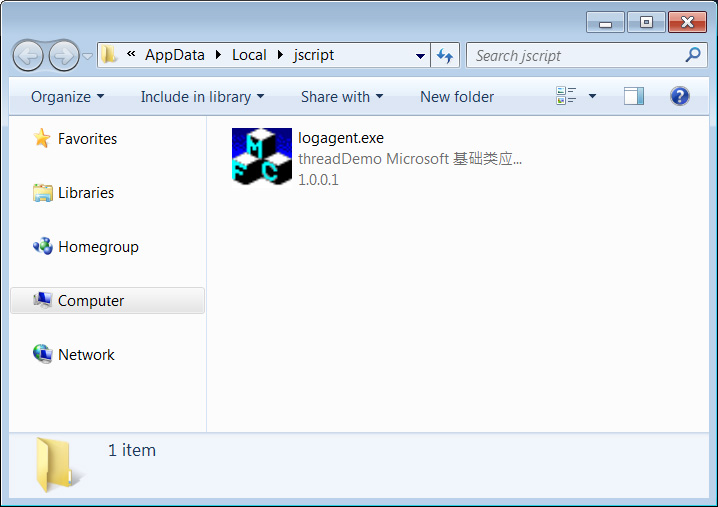
These malicious macros will download and install the Emotet malware on a victim’s computer, as shown below.
Why it’s necessary to recognize Emotet attachments?
Emotet is considered the most widely spread malware targeting users today. It is also particularly dangerous as it installs other malware such as Trickbot and QBot onto a victim’s computer.
While TrickBot and QBot perform malicious activity on their own, such as stealing stored passwords, banking information, and assorted other information, they also commonly lead to Conti (TrickBot) or ProLock (QBot) ransomware attacks.
Due to this, it is vital to recognize the malicious document templates used by Emotet so that you do not accidentally become infected.
NOTE:: This article is copyright by bleepingcomputer.com and we are using it for educational or Information purpose only